Anecdote:
“Since my school days, I have been fascinated by writing cryptic text, though intelligible. It all started with mirror-writing the teaching-feedback that was requested by our class teacher Tr. Jezuine. Once the feedback was read, the teacher called me and asked: “How did you learn this?” I was on cloud nine and replied, “it just happened only for you”, with a massive smile on my face. Later, I never thought of any secret writing for a while. It was only during the initial days of my teaching profession; I had the opportunity to read my classmate’s notes scribbled in a cryptic text which triggered further enthusiasm in me. So, during my postgraduate course, I started reading and presenting seminars on Cryptography and Security. This further led to deeper digging into the core of security aspects that also led to a trivial postgraduate project on key-establishment in wireless sensor networks. Later during the research period, I chose a new upcoming area – wireless sensor networks (broader domain), and contextual- and content- privacy (narrower domain) – privacy preservation in WSNs as my research topic.”
-Dr Manjula R
The Issue:
The significance: The privacy of individuals is being compromised gradually with the increasing popularity and rapid deployment of pervasive computing technologies. The benefits and conveniences offered by modern devices often lead people to neglect the dire consequences of possible privacy violations. Therefore, privacy risks should be taken into considerations while designing responsible technologies. One such technology that poses serious privacy risks is the Wireless Sensor Networks (WSNs). Despite the enormous benefits offered by WSNs to humanity, several issues need meticulous attention. Security and privacy are such issues in WSNs. For instance, the US military aims to adopt Internet of Things (IoT) enabled WSN. The usage of WSNs, Unmanned Aerial Vehicles (UAVs), tiny robots (nanoscale robots) are envisioned to transform the battlefield scenario. In particular, these digital devices and components are embedded in soldiers’ uniforms to collect the health status of the worriers and relay this information to a central controller, named the base station (BS). The BS is located near places where the internet is easily accessible. Nevertheless, WSNs are deployed in areas where it is challenging to have internet. However, this problem is easily solved with the amalgamation of WSNs and IoT. This comes with unwelcoming consequences. The unattended nature of these networks provides an attacker with physical access to the devices. The attacker may compromise the node and conduct illegal activities, say, mimic fake chemical leakages etc. Furthermore, the broadcast nature of the transmission medium gives access to the packets exchanged by the sensor nodes to anyone within the communication range. Consequently, adversaries may exploit these features of WSNs in order to launch attacks against the network and thus render all the potential benefits offered by this technology unusable. Hence, privacy preservation in WSNs is a significant issue that needs to be addressed to safeguard personal and private assets—soldiers or endangered animals etc.
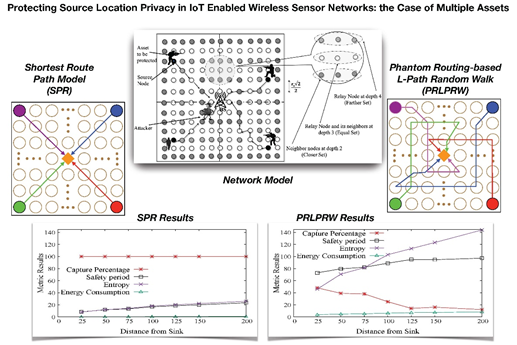
In a quest to provide countermeasures to such attacks, Dr Manjula R and her team are developing privacy preserved solutions with particular emphasis on routing in WSNs. Their recent research article titled “Protecting Source Location Privacy in IoT Enabled Wireless Sensor Networks: The Case of Multiple Assets” has been accepted for publication in a peer-reviewed journal – IEEE Internet of Things Journals. This work is co-authored by Prof. Raja Datta, IIT Kharagpur and Mr Tejodbhav Koduru (studying in 5th semester in dept. of CSE, SRM University AP). The SCI-indexed journal has an impact factor of 9. 396. The team is also focusing on the development of new countermeasures to mitigate eavesdropping attacks in WSNs.